Week Review 10/20/2023
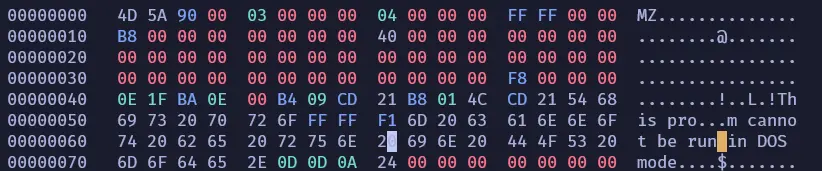
Getting GPIO on Adafruit Py QT Working
Getting the GPIO working on the Adafruit Py QT has been a challenge. This week I was finally able to do it using the Arduino IDE.
I learned I had been using the wrong documentation for the board. It uses a SEEED Xiao footprint, but it is not compatible with the software.
I was able to find the documentation made specifically for the Adafruit Py QT and it made the process much smoother.
Arduino
The Adafruit documentation has a guide for setting up both CircutPython and Arduino.
The long and short of the Arduino guide, is you need the Expressif ESP32-S2 board installed in the Arduino IDE. The SEEED Xiao board does not work for the Adafruit Py QT even though the product description says they are compatible.
Once I downloaded the board I tested making a GPIO pin output high for half a second, then output low for another half second. It worked and I have had sucess in minipulating all the pins.
Note on ESP32-S2 Bootloader
The bootloader for the Adafruit Py QT and ESP32-S2 chips in general are not write protected. You need to reinstall the bootloader using esptool after running Arduino code on the board.
Setting Up Communication on the Board
I have been researching different methods of storing and sending data from the microcontroller back to the surface station. Currently I am planning on using Websockets for communication and EEPROM for storage.
I chose Websockets over sockets for communication because of the libraries available and the microcontroller I am using. From my very light research I did, it seems the Websockets library is much more complete and user friendly than the sockets library.
I am using the Adafruit Py QT for the project has a 240MHz clock cycle, 2MB of PSRAM, and 4MB of flash which gives more than enough overhead for WebSockets over sockets.
EEProm allows you to store information in ROM (its a misnomer, you can write to it) on Arduinos without needing an entire file system. I am going to need to store the depth measurements in 5 second intervals, so a full filesystem is really not necessary.
Auditing the Websockets Library
I like to do some light auditing of any library that I am using. I want to make sure the code I am writing is not doomed from the start, and I see it as my way of contributing to the open source community.
I took a look at the code for the Websockets library and was very pleased to see that, unlike the radio library I used earlier, it properly sizes buffers and stops buffer overflows.
The code overall in the ArduinoWebsockets library, and by extension the TinyWebsockets library, is very well written, understandable, and as far as I can tell secure.
Antivirus Research
On my free time at home I have been testing how Windows Defender remembers malware on a given machine. I have found that once the malware is detected by Windows defender it only stores a hash of the file, and flipping one bit stops it from remembering that.
Flipping a bit in an executable seemed like it would be an issue to me at first, but windows gives a lovely buffer in each .exe file that lets people running it in DOS mode know that it will not work.
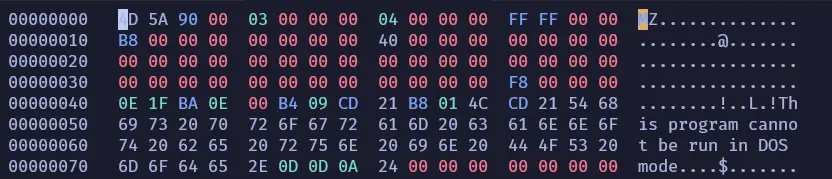
You can change the text in this buffer and it does not effect the execution of the program unless you were to actually run it in DOS mode.
Since it is such an obvious place to establish polymorphism, I assumed that it would flag antivirus to change that section of the binary. In my testing however it does not. I am surprised this is not used more often because writing code to edit that part of the binary is extraordinarily simple.